Recently I learned from the news that my mobile phone carrier’s data had been stolen for the second time in as many years. The company didn’t realize it until ten months after the breach, when the stolen data started appearing for sale on the Internet. Allegedly no credit card data was stolen, just names, addresses, birthdates, phone numbers, email addresses, and social security numbers. Why do criminals want this information? One reason is because it gives them what they need to steal your identity with the goal of making purchases in your name, or getting credit cards in your name.
While the credit bureaus have done a less than stellar job of protecting your credit, it is possible to make it harder for thieves to access by the process of freezing your credit record. This process makes it impossible for anyone to access your credit information unless you unlock it. That’s a slight inconvenience for you, but a real impediment for hackers. But stealing identity is not the only reason they want your information.
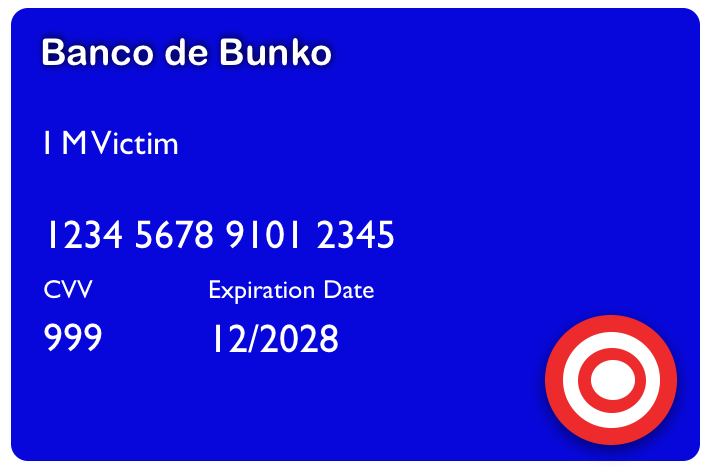
After a data breach, the stolen data is sold to brokers who operate on the dark web, that portion of the Internet that is not visible to normal browsers. There are online stores where the information is then re-sold piece by piece. Credit card numbers are sold for absurdly low amounts, because they are good only until the cardholders report them stolen. Passwords are still useful, because there are still so many users that use the same password on every website. So if Bubba’s Amazing T-Shirt site gets hacked, and your password is harvested, it could be much more valuable if that same email and password is used to access your bank. But there is also great value to a thief for the data that you would expect to have the least value: your name, address, phone number, and email. How? So it can be used for phishing.
Give a man a fish, and you feed him for a day. Teach a man to phish and he’ll rob you blind.
To see how phishing works I’ll tell you about the experience of my next door neighbors, Mike and Mona (real people whose names I’m withholding). Really great people, maybe you know them. So last year Mike gets this email that seems to be from the company that provides his phone and Internet service. It’s a special promotion. If he prepays for both services for 6 months they will give him $800 in eBay gift cards. He puts in his credit card and goes for the deal. Mona is skeptical. That doesn’t seem right. After a little arguing, he calls his credit card company to cancel the charge. It’s too late. The scammers have already purchased the gift cards with his card and redeemed them. There is no way to cancel the charge. What Mike didn’t realize is that the email he received did not come from his phone company. Sure, it had all the right logos and looked like their website, but that can be easily faked. The red flag is a deal that seems too good to be true.
Several months later Mona got a text message on her phone. It said that her PayPal account was going to be billed $1,000 for a shipment. A customer service phone number was included in the text, so she called it. The person who answered said she could cancel the order, but would need Mona’s help to do it. Then the agent uttered the deadly phrase “Go to your computer.” Following the instructions she got on the phone, Mona hacked her own computer. By going to the website as instructed, malware was installed on her computer, locking it so it could no longer be used unless she paid a fee for the unlocking password. Fortunately a big box computer store was able to remove it, and she didn’t lose any money. Because Mona was in a panic when this text came in, she immediately rushed to call the number without noticing a few red flags:
Mona does not have a PayPal account. It’s hard to bill an account you don’t have.
The voice that answered the phone was heavily accented, and obviously not a native English speaker. Most of these phishing operations are outside of the US, to avoid prosecution.
Cancelling the fictitious order should have been possible without Mona going to her computer at all, particularly since she never placed any order.
These days almost any phone number can also receive text messages. This has opened up a new type of phishing scam. You may receive a text message with like this: Hi, it’s Mary. I’m caught in traffic. Can you pick up Bobby from school? He’ll be scared if I’m not there, and he knows you. Thanks so much!
Of course you don’t know Mary or Bobby. Clearly this message was meant for someone else, but what will happen if you don’t let Mary know she sent it to the wrong number? So you quickly reply that it’s a mistake and then you get this:
Oh I’m so sorry, you saved my son from something terrible. Thank you so, so much!
Well that’s good, job done. But the next day: Hi, it’s me Mary. I just want to thank you again for your kindness. There are so few good people like you. I’m a single mom, and it’s hard to meet new people between work and my son. I’d really like to do something nice for you. Can I send you some flowers?
Well now you feel kind of sorry for Mary. She’s struggling. You reply that no flowers are necessary. Pretty soon you’re getting a dialog going with “Mary”, and before you know it she’s going to be about to be put out on the street because her son got sick and she can’t pay the rent. She has no family, and just needs $500 to get by until her next paycheck.
This is a new version of the Nigerian prince email ruse, the one where your help is needed to get money out of the country. Instead of a promise of a share of money that will never come, you get a sob story to make you send money without thinking you’ll get anything back. The “Mary” you are texting with is perhaps the same guy who was sending the Nigerian emails previously. That scam quit working, so they cooked up a new one. Buying a few hundred breached phone numbers makes it easy for them to approach a lot of people for a very small amount of money. The criminals can make lots of money, just as they did with the emails, and they are all located in places that are out of reach of the law.
Like many of us, I buy a lot of things online. If an online merchant is hacked and data is stolen, credit cards are a favorite target. The thieves often sell the numbers to shady merchants on the dark web. Using software tools, the stolen card numbers will be used to make small purchases as “test charges”. Each one that goes through verifies that the card has not been reported stolen. Recently I was reviewing charges on one of my cards and I saw a charge for $1 to a local merchant that I had never visited. I suspected it was a test charge, and immediately locked the card. Some credit card companies offer the capability either by visiting the card website, or using the feature in the card app. I called the card issuer, and a new card is on the way. It’s a good idea to know in advance whether you have the ability to lock or “freeze” your credit cards.
With so much information being stored on the Internet, having your information caught in a data breach will almost certainly happen at some point. How can you protect yourself? Here are a few suggestions:
Monitor your credit cards by checking the transactions often. If you see a charge that you did not make, freeze the card if you can. Then call the issuing card company immediately. Use the phone number for fraud that you find on the card website.
If you get an email or text regarding something you did not order, do not click on any link in the message. Don’t call any phone number in the message either. Check your credit cards to see if a charge has been made. If the message references shipment from a company, go to that company’s website to see if there is an open order. Again, don’t use the link in the message. Instead open your browser and Google for the company site. If you have never made an account at that site, look for a phone number you can call to check for an order.
If you get a text message from a number or person you don’t recognize, do not respond. If it’s obviously spam (e.g. Vote for Ima Grifter for City Council) you may be able to report it as spam right there on your phone.
Some credit cards (e.g. Discover) will scan the dark web to see if your information is there. They will alert you if anything relating to you is found.
Most credit cards and banks will also allow you to set up alerts for charges or withdrawals over a certain amount of money. This gives you an instant alert.
If you get an email from a website asking you to change your password, do not click on the link in the email to do that. Instead go to the site directly by typing the address into your browser and change it there. A scammer can set up a fake website that asks for your existing password before changing. That’s what they want.
Beware of emails that have awkward wording. That usually means the sender is not a native speaker, and may be up to no good. Multiple spelling errors are also a red flag.
Don’t rely on paid services to protect you. Most of them just monitor your credit report, which you can do yourself for free. Some are even operated by the same credit reporting agency that has a poor performance record. This also holds for the “free” monitoring service that a breached company may give you for some period of time, after they lost your information.
Years ago, on the TV show Hill Street Blues, the sergeant briefing the police would close his daily briefing with a phrase that we should all heed:
Let’s be careful out there!